As our reliance on digital platforms intensifies, the menace of website spoofing becomes alarmingly prevalent. Fake websites that mimic reputable businesses proliferate, drawing individuals into data theft traps with fraudulent emails, deceptive text messages, and bogus business profiles.
The start of 2023 witnessed an alarming report from Digital Information World highlighting an increase in sophisticated methods of cyber deception, including fake versions of popular sites. Crafty scammers are now spoofing ChatGPT websites and associated apps to pilfer data from the unaware quietly. In response, Meta has reportedly neutralized close to 1,000 harmful URLs connected to ChatGPT. Such manipulations don’t just trigger technical concerns; they strike deep at the heart of digital trust.
Join us as we venture into the dark ocean floor of the internet, where websites are not always what they seem, and website spoofing is aspiring to become “the Great Pacific garbage patch” in a vast sea of cyber threats.
The Spoof Is Out There
Website spoofing, a sophisticated form of phishing attack, poses a dire challenge to our digital safety. As our reliance on the internet for daily tasks balloons, so do these incidents of digital deceit, with individuals and corporations both bearing the brunt.
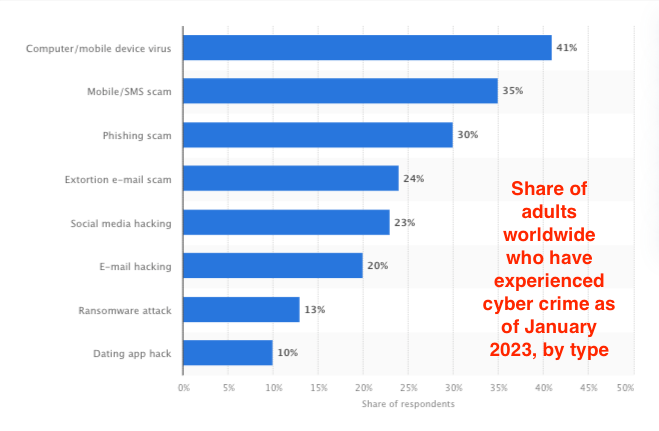
A sobering 30% of adults worldwide were ensnared by phishing in 2022, and a separate survey indicated that over 83% of participants had succumbed to a successful phishing incursion within that year. As 2023 unfolds and online services become more entrenched in our lives, the lurking dangers of cyber malefactors become undeniable.
However, this represents just a glimpse of the broader cybersecurity challenge spoofing offers.
The goal of most spoofing attacks is the illicit acquisition of data, and while that can be devastating to an individual, the costs are astronomical for a corporation. IBM’s 2023 data breach report underscores the gravity of this situation, putting the average potential price of such breaches at a staggering $4.91 million.
Website Spoofing Fraud Demystified
But how exactly does this all work?
Website spoofing capitalizes on HTTPS’s security protocols, ingeniously coaxing individuals into surrendering private data. With painstaking precision, cybercriminals erect faux websites mirroring genuine ones, down to familiar icons like the green padlock and the “https://” prefix.
The intention? Mislead users into thinking they’re on a safe platform. Users enter personal information or corporate access credentials; before they realize it, they’ve been hacked.
Several tactics are deployed in this subterfuge: In URL phishing, crafted URLs almost indistinguishable from genuine ones trick victims into believing they’re on a legitimate platform. Clone websites are a near-perfect replica of authentic websites, complete with logos and layouts, that hoodwink users about the site’s genuineness. In Man-in-the-Middle Attacks, hackers discreetly intercept communications between a user and a website server, tapping into critical data undetected with HTTPS spoofing aiding their cover.
More new spoofing scenarios are discovered as time passes—and that’s bad news on two fronts. One, when a new spoofing method is discovered, it’s too late for whoever was defrauded. And two, attacks are getting more sophisticated, and targets are getting bigger.
Loonie Thieves Strike Canadian Banks
Even trusted financial institutions aren’t safe from website spoofers these days.
In March 2023, Coast Capital Savings, a credit union in Canada, issued a fraud alert after a scam website duped members. The scam website was a spoofed version of the Coast Capital Savings website, which looked identical to the real website. However, it was actually hosted on a different domain and designed to steal members’ login credentials.
Cyber attackers emailed Coast Capital Savings members with links to the spoofed website. The emails, designed to look like they were from Coast Capital Savings, claimed that members needed to update their login credentials. When members clicked on the links in the emails and entered their login credentials on the spoofed website, their credentials were stolen.
The stolen login credentials were used to access members’ savings accounts and steal money, leaving customers broke—and criminals flush with Canadian loonies.
Beyond the clear financial implications, such incidents shake our faith in digital ecosystems. They make individuals second-guess every digital step, and companies confront enduring reputation damage.
The Solution? Proactive Defense Measures
Coast Capital Savings took steps to protect its members after the fraud was discovered, including sending alerts, blocking the spoofed site, and working with law enforcement. But it wasn’t enough to solve the bigger problem.
Reactive methods, though essential, are not enough. And it’s not just about deploying sophisticated software defenses; human awareness is equally vital. Employees need to be educated sentinels versed in identifying lurking threats.
Intersecting with this is the challenge of complying with and leveraging cyber regulations. Collaborative intelligence sharing, spanning industries and borders, emerges as a potent weapon against borderless spoofing threats.
Enter Memcyco, a solution designed for the evolving challenges of our times. Unlike traditional spoofing defenses like threat intelligence/brand protection solutions (and, to a lesser degree, safe browsing solutions), Memcyco is explicitly designed to thwart website spoofing.
Memcyco offers real-time defense against website spoofing and brandjacking by integrating an active tracking sensor directly into genuine websites and includes a digital watermark authenticating the website. Its comprehensive solution delivers instant attack detection and notifications, detailed forensics, and advanced mitigation strategies, ensuring protection during the crucial period between creating a fake site and removing it.

Eran Tsur is CEO of Memcyco. He writes about the growing impact of digital impersonation, phishing, and account takeover attacks on global enterprises. His insights focus on how organizations can move beyond traditional fraud detection and adopt earlier detection strategies to stop impersonation-driven attacks before customer accounts and brand trust are compromised.