Predictive, real-time customer ATO prevention
Know which customer accounts will be targeted by phishing-related scams, reduce customer ATOs by over 50% and slash incident-related OPEX
Introduction
Most organizations discover an account takeover after a customer calls to report unauthorized activity. By that point, credentials are gone, funds may be drained, and the attacker has moved on. The core problem isn’t detection speed. It’s that most tools are built to catch fraud after authentication, not before it.
An effective account takeover solution must intervene during the credential theft phase, before an attacker ever reaches your login portal. That means detecting live phishing and impersonation attacks in real time, identifying individual victims as they interact with fake sites, and disrupting attacker workflows before a single credential is compromised.
This guide covers how ATO attacks work, where legacy tools fail, what to demand from a modern solution, and how preemptive detection changes the outcome.
The ATO Problem No One Is Solving Fast Enough
ATO fraud losses are projected to hit $17 billion in 2025, up from $13 billion the prior year, with attacks surging 122% in fintech, per the Sift Q3 2025 Digital Trust Index. Fraud budgets keep growing. Losses keep climbing.
The reason is simple: most tools detect ATO after credentials are already stolen. By then, the damage is done.
This guide covers ATO anatomy, why legacy tools fall short, and what real preemptive protection actually requires.
What Is an Account Takeover Attack?
Account takeover (ATO) is the unauthorized acquisition of a legitimate user account through credential theft or session compromise. Once inside, the attacker operates as the authenticated user, invisible to most security controls.
The financial damage is significant. ATO fraud cost consumers $15.6 billion in 2024, and Sift’s Q3 2024 Digital Trust Index recorded a 24% year-over-year rise in ATO attack rates.
As banking, eCommerce, travel, and telco moved online, the attack surface expanded. Attackers followed.
Credential Stuffing: Automation at Scale
Bots test billions of stolen credentials against live accounts at machine speed. The Thales 2025 Imperva Bad Bot Report found credential stuffing drives 78% of all ATO attacks.
Rate limiting and CAPTCHA can’t keep pace.
Phishing and Digital Impersonation: The Human Layer
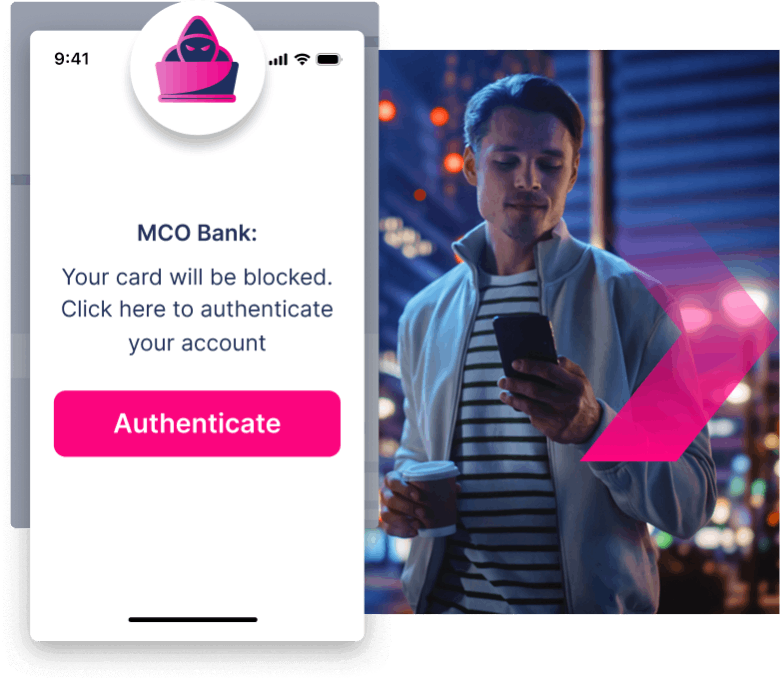
Attackers clone legitimate sites and spin up lookalike domains to harvest credentials directly from victims. The victim hands over their login details willingly.
Your organization has zero visibility while it happens.
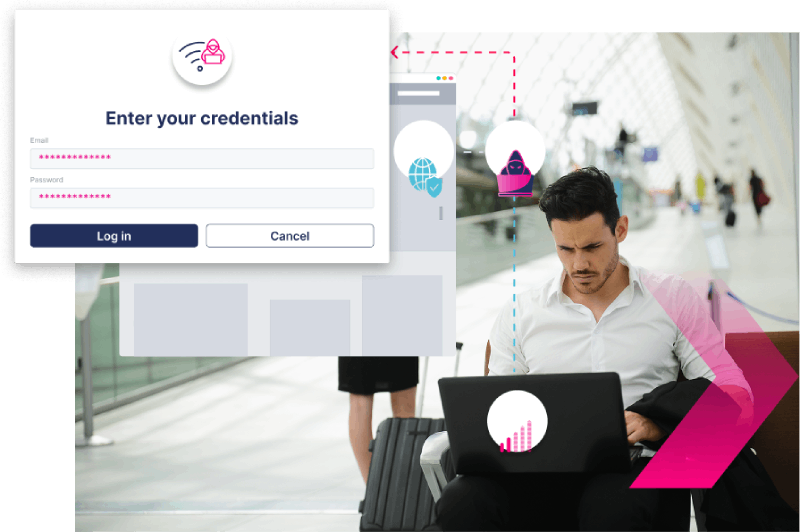
Man-in-the-Middle (MitM) and Session Hijacking
MitM and adversary-in-the-middle (AiTM) proxies intercept live sessions and steal authenticated tokens, bypassing MFA entirely. Microsoft confirms AiTM kits now operate at scale.
MFA alone isn’t enough.
Why ATO Is Accelerating:
The Forces Behind the Surge
Three structural forces are making ATO worse, not better.

First, stolen credentials are practically free. Billions of username-password pairs circulate openly on dark web markets and Telegram channels, slashing the barrier to entry for attackers. Second, attack tooling is commoditized. ATO-as-a-service kits and AI-powered phishing generators cost a few hundred dollars, putting sophisticated campaigns within reach of low-skill actors.
Third, digital transformation has widened the attack surface. Financial accounts offer direct monetary access. eCommerce platforms store payment methods. Airlines and hospitality brands hold loyalty currencies that are easily liquidated. Telcos enable downstream SIM-swap fraud.
The numbers reflect this. ATO attacks surged 250% targeting loyalty programs and gift cards, per AI Connects’ 2025 Account Takeover Trends. Losses are projected to hit $17 billion in 2025, per Sift’s Q3 2025 Digital Trust Index. More digital channels means more exposure, not less.
Latest Podcast Episodes
The MemcycoFM Show: Ep 24 – Real-Time Remote Desktop Takeover Detection and Mitigation
The MemcycoFM Show: Ep 23 – Real-Time MitM Protection and ATO Prevention Strategy
How Legacy ATO Solutions Fall Short
Every legacy ATO tool shares the same fundamental flaw: it assumes the organization will catch fraud after credentials are stolen.
That assumption is costly. By the time most tools fire an alert, the attacker is already inside.

- Email security gateways block known phishing domains but miss real-time spoofed sites targeting your customers right now.
- Post-login behavioral tools detect anomalies after credentials are compromised, adding friction without addressing the upstream attack.
- MFA and identity controls are strong, but man-in-the-middle techniques bypass them routinely.
- Traditional SIEM correlates logs well, but The Hacker News reports up to 30% of SOC analyst time is lost chasing false positives.
The problem isn’t that these tools are bad at what they do. It’s that what they do isn’t enough. The attack has already succeeded by the time they act.
Manual Fraud Monitoring and Rules-Based Systems
Rules-based systems flag suspicious logins after authentication succeeds. By then, the attacker is already inside. Constant manual tuning can’t keep pace with attackers who study and evade detection patterns.
Email Security Gateways and Anti-Phishing Tools
Email gateways stop malicious emails from reaching corporate inboxes. They can’t protect your customers on personal accounts, or when attackers reach them via SMS, social media, or SEO poisoning.
Scan-and-Takedown / Brand Protection Services
Scan-and-takedown services find fake sites and file removal requests. Takedowns take days. Attackers spin up replacement sites faster than registrars can act. The attacker always wins the time arbitrage.
Post-Login Behavioral Analytics and SIEM
Behavioral analytics catches anomalies after attackers have already authenticated. By then, credentials are stolen, customers are victimized, and your team is cleaning up damage instead of preventing it.
Dive Deeper Into ATO
How to Calculate the ROI of Brand Protection Software: A Framework for Security Leaders
What to look for in a modern account takeover solution
Every vendor will tell you they cover ATO. Most are telling half the truth.
When evaluating solutions, demand these six capabilities:
- Email security gateways block known phishing domains but miss real-time spoofed sites targeting your customers right now.
- Post-login behavioral tools detect anomalies after credentials are compromised, adding friction without addressing the upstream attack.
- MFA and identity controls are strong, but man-in-the-middle techniques bypass them routinely.
- Traditional SIEM correlates logs well, but The Hacker News reports up to 30% of SOC analyst time is lost chasing false positives.

The critical probe: what is the vendor’s mean time to detection for a live phishing campaign? Vague answers expose reactive tools.
Real-Time Attack Detection During the Credential Theft Phase
Ask your vendor one question: can you detect a phishing site that launched 10 minutes ago? If they hesitate, credentials are already being harvested.
Agentless Deployment and Low Customer Friction
No endpoint agents. No browser extensions. No end-user installation. Memcyco deploys via API, fits into your existing infrastructure, and adds zero friction for your customers.
Individual Victim Identification
Ask vendors directly: can you identify which specific customers visited a phishing site and submitted credentials during a live attack, before they attempt to log in?
Measurable ROI and Business Impact
Don’t accept vague promises. Ask vendors for documented fraud loss reduction, investigation time savings, and first-year ROI metrics from reference customers in your industry.
Integration with Existing Fraud, Authentication, and SIEM Systems
Your fraud, authentication, and SIEM investments shouldn’t operate blind. A modern account takeover solution enriches them with real-time attack intelligence that legacy tools can’t surface.
Proactive Attack Disruption
Ask vendors directly: does your solution watch attacks unfold or actively stop them? Feeding attackers decoy credentials and alerting victims in real time kills attacker ROI.
How Memcyco Stops Account Takeover in Real Time
Most ATO tools wait for credentials to be stolen. Memcyco intervenes before that moment.
Memcyco’s Proof of Source Authenticity (PoSA) technology infiltrates live phishing and impersonation attacks at the point of credential theft, identifies individual victims in real time, and injects decoy data to disrupt attacker workflows. It deploys agentlessly via API and integrates with existing fraud, authentication, and SIEM systems.
The outcomes are documented: 10x ROI within the first year, 50% fewer ATO incidents, and up to 90% reduction in investigation time. One CISO at a Top-10 North American Bank put it plainly: “They took our incident handling times from 72 hours to less than 1 hour and saved us millions every month.”
Datos Insights analyst David Mattei noted that Memcyco “provides financial institutions with visibility into fraud attempts before credentials are compromised, addressing a persistent blind spot in traditional security frameworks.” Frost & Sullivan’s 2025 Global Transformational Innovation Leadership Recognition echoed this: “Memcyco has launched a preemptive solution to detect and stop fraud before it occurs.” A $37M Series A in January 2026 confirms the market is paying attention.
How PoSA Works: Infiltrating the Attack Before Damage Occurs
PoSA infiltrates live phishing attacks targeting your web assets. It injects decoy credentials into the attacker’s harvesting workflow, making stolen data useless. It identifies individual victims, triggers real-time Red Alert warnings, and requires no end-user installation.
What Memcyco Surfaces That Legacy Tools Cannot
Legacy tools surface domain alerts and post-login anomalies. Memcyco surfaces the victim sitting on a live phishing site right now, the attacker’s infrastructure, and session-level data fed directly into your SIEM and fraud stack.
Crush Atos Earlier, and Keep Them Crushed Longer
Discover why global brands replace their previous solution with Memcyco

ATO Prevention Across Industries: Use Cases
ATO doesn’t look the same in every industry. The attack vector shifts, the asset at risk changes, and the cost of a missed detection varies. Here’s how it plays out across four verticals.
- Financial services: A phishing site mimics a bank’s login portal. Customers enter credentials. Legacy tools flag the site days later. Memcyco detects the live attack, identifies each victim in real time, and alerts fraud teams before a single account is drained.
- eCommerce: Credential stuffing hits loyalty accounts overnight. Points are redeemed before morning. Memcyco intercepts the attack as it unfolds, not after the cart empties.
- Airlines: Frequent-flyer accounts are prime targets. Stolen miles convert to cash fast. Memcyco spots fake login pages and disrupts attacker workflows before redemption occurs.
- Telcos: SIM swap fraud starts with account access. Memcyco identifies compromised sessions in real time, cutting the window attackers need to escalate.
Financial institutions: credential harvesting and banking ATO
Financial services account for 22% of all ATO attacks (Thales 2025 Bad Bot Report), and fintech ATO surged 122% year-over-year (Sift Q3 2025 Digital Trust Index). Banking customers are the most targeted victims in the credential economy, and the gap is widening.
Airlines and travel: frequent flyer fraud and accommodation partner ATO
Frequent flyer miles are a liquid, largely unregulated currency. Attackers drain them fast. Memcyco detects the fake loyalty portal at launch and stops the harvest before a single mile moves.
eCommerce: loyalty points, stored payment methods, and account fraud
ATO attacks targeting loyalty programs surged 250% in 2025. Memcyco detects phishing sites in real time, warns victims before credentials are submitted, and feeds attackers decoy data.
Telcos: SIM Swapping, Account Takeover, and Downstream Fraud
Telco ATO doesn’t stop at the account. A hijacked phone number bypasses MFA everywhere, turning one compromised portal into cascading fraud across banking, payments, and beyond.
How to Evaluate and Implement an ATO Solution
Evaluating an ATO solution follows three phases.
- Build the business case first. Quantify current losses: fraud reimbursements, investigation hours, and customer churn from compromised accounts. Those numbers make the ROI conversation hard to dismiss.
- Run a structured vendor evaluation. Demand real-time detection, victim-level visibility, and agentless deployment. Test integration with your existing SIEM, anti-fraud, and authentication stack. If a vendor can’t demonstrate live attack disruption in a proof of concept, move on.
- Deploy with integration in mind. Memcyco connects via API with no end-user installation and no friction for your customers.
Ready to see it in action?
Building the Business Case for a Modern ATO Solution
Start by benchmarking your current mean time to detect a live phishing campaign targeting your customers. IBM’s 2025 Cost of a Data Breach Report puts average breach identification at 241 days. That gap is your business case.
Vendor Evaluation: Questions That Separate Preemptive from Reactive
Ask vendors exactly when they detect a threat: before credential submission, or after? Demand documented mean time to detection, victim-level visibility, and active disruption capabilities. Memcyco publishes a detailed RFP guide for evaluating ATO fraud solutions covering every criterion.
Deployment and Integration: What to Expect
Memcyco’s agentless model requires no end-user installation. APIs connect directly with anti-fraud platforms, authentication systems, and SIEM tools. Organizations move from evaluation to active protection in days, not months.
Key Takeaways: What a Modern ATO Solution Must Do
- ATO losses reached $17B in 2025, with financial services attacks up 122% year-over-year
- Legacy tools detect fraud after the damage is done
- Modern solutions must intercept attacks at the credential theft phase
- Identifying individual victims isn’t optional. It’s the foundation of effective response
- Proactive disruption separates preemptive platforms from reactive ones
- Agentless deployment and API integration mean fast time to value
- Proven ROI: 10x returns, 50% fewer incidents, 90% less investigation time
See preemptive ATO protection in action.
Stop ATO Before
It Reaches Your
Customers
Most ATO solutions arrive after the breach. Memcyco stops it before credentials are touched. Backed by a $37M Series A, request a demo and see it live.
Conclusion
Stopping ATO fraud requires more than faster detection after the fact. It requires intervening before credentials are stolen. A modern account takeover solution must operate during the attack phase, identify individual victims in real time, and actively disrupt credential harvesting. Legacy tools built around post-login signals will always be one step behind.
See How Memcyco Stops ATO Before Credentials Are Stolen
Most ATO solutions wait until after the damage is done. Memcyco infiltrates live attacks, identifies individual victims in real time, and disrupts attacker workflows before a single credential is compromised. See it in action.
Predict and prevent ATOs
Reduce ATOs
50%
Achieve MTTD of
Zero
Cut expenses by
$Millions
Already solved MitM attacks? Solve more


Man in the Middle (MiTM) Protection

Remote desktop takeover


Credential Stuffing

Fake e-shops, purchase scams, gift card scams

Get a Custom Demo
See it in action and discover why others switch to Memcyco
Get a demo to learn how Memcyco customer :
-
Identify individual scam victims in real-time
-
Predict and preempt ATO incidents
-
Deceive threat actors
Frequently asked questions
What Is an Account Takeover (ATO)?
An Account Takeover (ATO) refers to unauthorized access to a customer’s online account. This form of identity theft allows cybercriminals to conduct unauthorized transactions, withdraw funds, and access sensitive personal and financial information of the customer. It directly impacts customer trust and can lead to significant financial losses.
Why Is Real-time Account Takeover Prevention So Important?
Real-time prevention is vital for protecting customer accounts from unauthorized access. It provides immediate detection and response capabilities that stop fraudsters in their tracks, thereby preventing them from exploiting stolen credentials. This is crucial in maintaining the integrity of customer transactions and safeguarding sensitive information.
Why Are ATO Attacks Still a Massive Threat for Many Businesses?
ATO attacks pose a massive threat due to the increasing reliance of customers on digital services for banking, shopping, and personal data management. These platforms are lucrative targets for attackers looking to exploit weak security measures and gain access to a wealth of personal data.
How Do Account Takeovers Happen?
ATO primarily happens through techniques such as phishing, where customers are deceived into providing login information, or through malware that records keystrokes. Attackers also use credential stuffing, applying stolen credentials to breach multiple accounts, taking advantage of customers who reuse passwords across services.
Who Do Account Takeovers Impact?
ATO impacts customers by compromising their personal and financial information, which can lead to unauthorized purchases, identity theft, and financial loss. The repercussions extend to businesses, resulting in lost customer trust, reputational damage, and potential financial and legal penalties.
How Can Businesses Prevent More ATOs?
Businesses can enhance their defenses against customer ATOs by implementing Multi-Factor Authentication (MFA), using advanced security solutions like real-time threat detection systems, and by conducting regular security awareness training. These measures help in identifying and mitigating threats before they impact customers.
What Measures Can Businesses Take to Protect Customers from ATO?
To protect customers, businesses should enforce robust password requirements, enable MFA, regularly update security systems, and monitor customer accounts for unusual activities. Additionally, educating customers on the importance of secure online practices and how to identify phishing attempts is crucial.
Why Should You Use a Real-Time Account Takeover Protection Solution?
A real-time ATO protection solution is essential because it monitors customer accounts for signs of unauthorized access continuously. This allows businesses to respond instantly to potential threats, safeguarding customer data and preventing financial losses associated with ATO incidents.
What Account Takeover Techniques Do Fraudsters Use?
Fraudsters employ several techniques targeted at customers, including phishing emails that mimic legitimate requests, credential stuffing with previously breached data, and more targeted attacks like SIM swapping to intercept one-time passcodes. Understanding these techniques helps businesses better protect their customers.
How Much Does It Cost to Remediate ATO Incidents?
The cost of remediating ATO incidents primarily involves direct losses incurred through fraudulent transactions and the operational costs of securing compromised accounts. Additionally, indirect costs such as customer support, legal fees, and efforts to rebuild customer trust can be significant.
By focusing on customer-centric aspects of ATO, these responses aim to provide businesses with clear and actionable insights on protecting their clients and maintaining the security and integrity of their services.