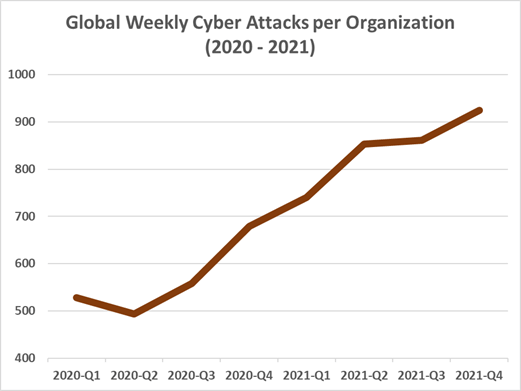
The vast majority of customers (96%) list an exceptional customer experience as one of the critical factors in their choice of loyalty to a brand. But providing such an experience became much more challenging in the wake of the pandemic, where cybercrime spiked as customer-facing businesses quickly accelerated their digital experiences, as shown in the graph below. Unfortunately, this period of high traffic and remote work has helped to perfect the methods of malicious threat actors.
Today, 25% of companies receive branded emails that are spoofed or brand impersonation attempts. The challenge now is for businesses to deliver a secure customer experience that is positive, secure, and frictionless at every stage. This challenge is particularly crucial in the competitive online landscape, where the race to provide the best customer experience is on.
Traditionally, the customer experience and the steps involved (aka, the customer journey) were owned by marketing, sales, and customer support. But in the post-pandemic era, the security department must work together with other departments to create a customer journey that is safe and frictionless, resulting in loyal and happy customers.
What’s a customer journey, and why does it matter?
The customer journey describes the online interactions the customer takes from the moment they hear about your business to the point they decide to become your customer–and hopefully, it continues to the point where they become loyal, returning customers.
These online interactions, or touchpoints, include online ads, email newsletters, social media posts, customer login portals, and even checkout and payment forms for eCommerce brands and online banks. Together, these interactions across multiple departments work to drive sales and sustain your relationship with customers.
That’s why the customer journey directly influences business growth and revenue. Forrester states that businesses that successfully deliver a positive customer experience boast 5.7 times more revenue than competitors unable to achieve this. At the same time, this experience must also be safe.
The dark side of the customer journey
Unfortunately, while these multi-channel touchpoints allow more opportunities for customers to familiarize themselves with your brand, they also significantly increase the possibility for malicious threat actors to destroy your customer experience.
Brand impersonation, phishing, identity theft, website cloning, and business email compromise are just a few methods these threat actors employ to target your customers.
These attacks have increased in frequency and complexity as businesses accelerated their digital experiences during the global pandemic.
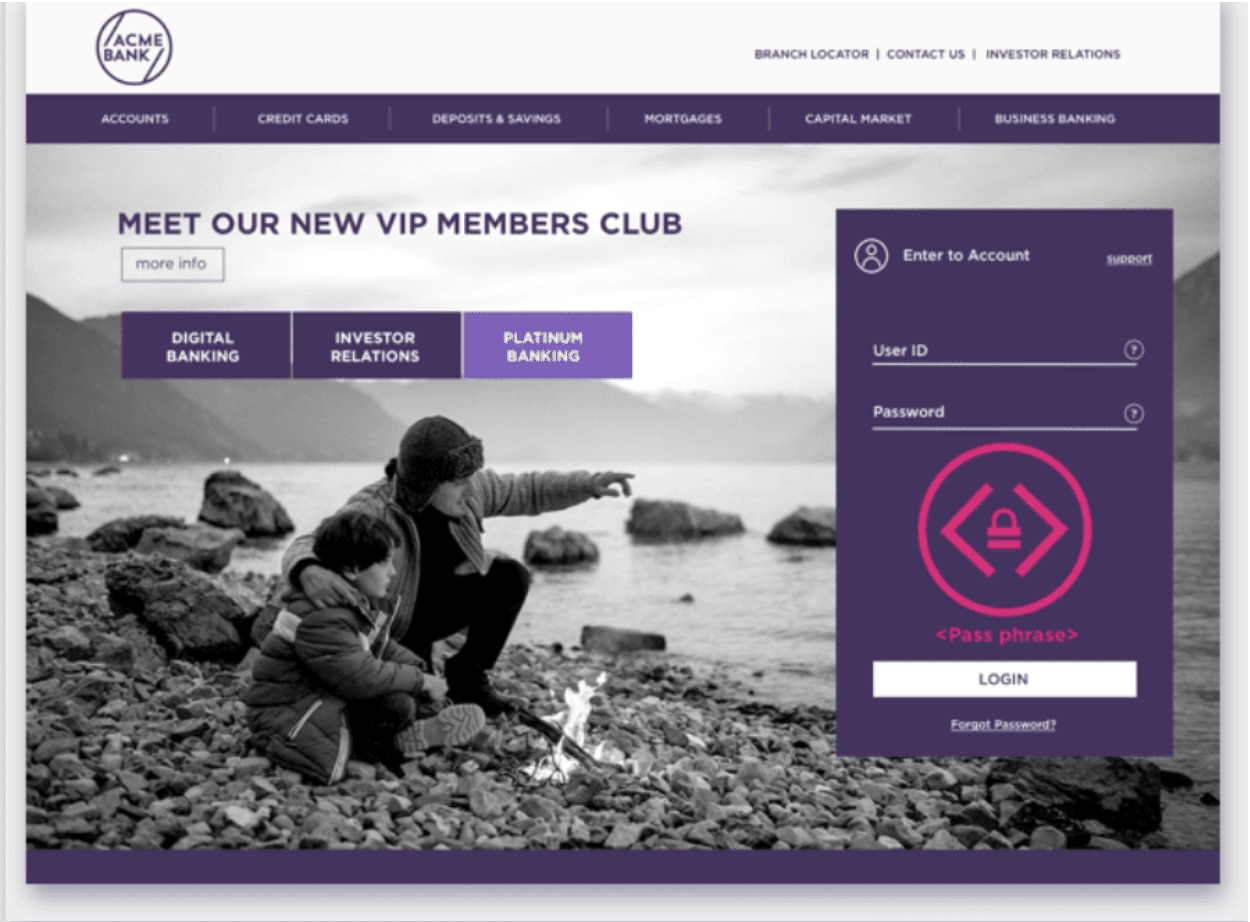
Example of a cloned site with Memyco’s alert system
For example, consider that:
- Brand impersonation has risen by more than 360% since 2020
- Brand fraud in 2021 was 15 times higher than in 2020
- One-quarter of all email phishing attacks in Q4 2021 spoofed UPS or DHL
Customers are still falling prey to these scams. One in three is likely to click on links in phishing emails. Almost half (45%) of employees surveyed click on emails they suspect are phishing or other scams “just in case it’s important.”
These unsecured touchpoints result in security breaches, exposed company sensitive data, and a loss in revenue and customer trust in your brand.
The 5 customer journey stages every brand should know
As the saying goes: “The best defense is a good offense.” Security professionals must understand the different stages of the customer journey to work with the various departments in your business that help to deliver an exceptional and safe customer experience.
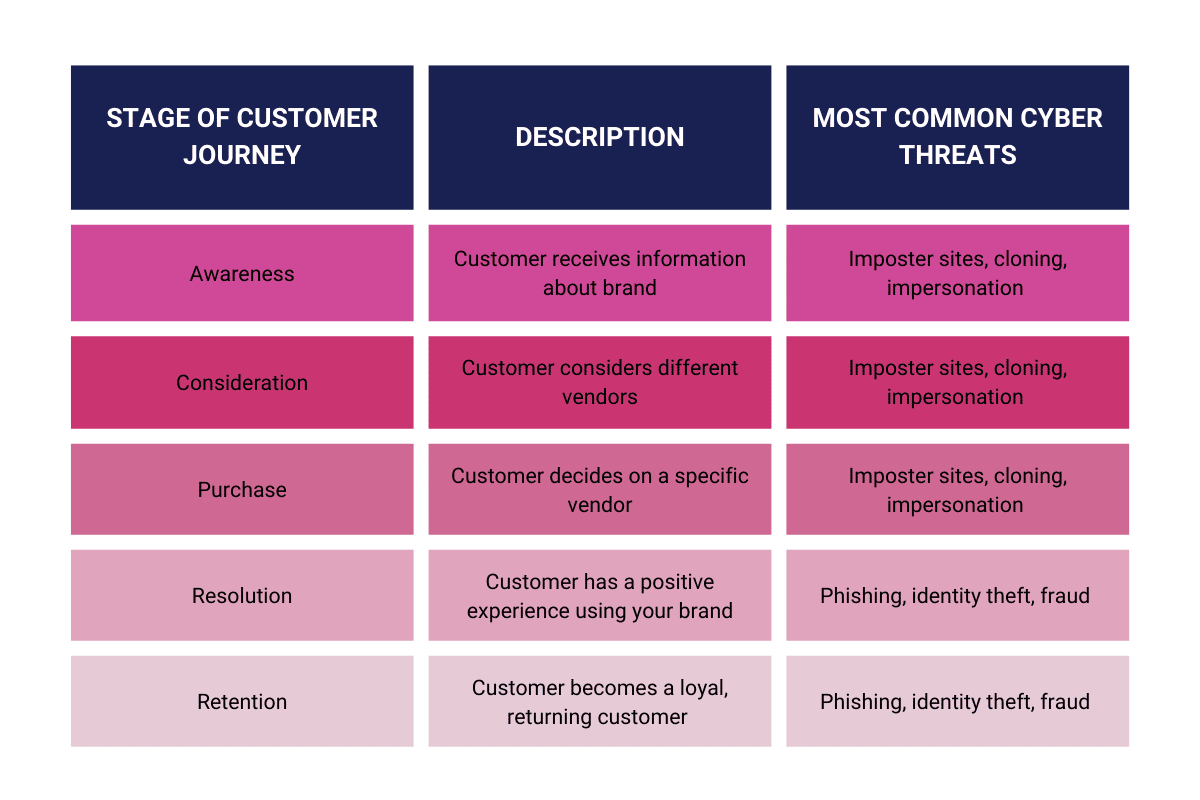
Here are the major steps the customer takes before finally becoming a loyal customer, and the possible cyber threats they might encounter:
1. Awareness
A customer may search online for a solution to a challenge they face and stumble upon your brand’s blog, ebook, or other marketing material. This stage opens an opportunity for the customer to start recognizing your brand. Customers must know that they are visiting a safe and secure website and can gather information without being attacked by malicious threat actors. One incidence of a cloned site or phishing attempt, and they might never revisit your website.
2. Consideration (of product/solution)
At this point, the customer understands the general solution to his problem but is weighing the pros and cons of each brand’s offer. Brands, on the other hand, may be luring them in through things such as price, discounts, and coupons–but although these tactics may help a customer move to the decision stage, online coupons can also be falsified by scammers to compromise their credit card information.
3. Purchase
At this stage, the customer decides to purchase and chooses your brand. For instance, a customer might need a mortgage and is now examining which mortgage would have the lowest monthly payment, interest rate, etc. A frictionless onboarding experience (i.e., the online mortgage application form) that also ensures the protection of the customer’s personal information can tip the scales in your brand’s favor. Customers must have a method to ensure that the information they receive is accurate and legitimate, not a cloned or imposter site.
4. Resolution
The customer now experiences your brand or tests your product and has a positive experience. They may become an advocate of your brand, leave positive reviews, and share their experience with friends and family, bringing you new customers.
5. Retention
The customer becomes a loyal, returning customer. Ecommerce companies often use loyalty programs to push customers into this customer journey stage. Unfortunately, loyalty programs are also a golden opportunity for phishing, identity theft, and customer fraud.
 Source: TheWiseMarketer
Source: TheWiseMarketer
Ensuring a Secure and Frictionless Customer Experience
Security can be another substantial impediment for customers at every customer journey stage. But it doesn’t have to be. As the CEB aptly put it: “Customers encounter predictable impediments at each buying stage. Suppliers should anticipate and remove these to simplify the process.”
Brands know it costs more to acquire new customers than to retain old ones. MemcyCo POSA (Proof of Source Authenticity) can help security teams deliver a secure and frictionless customer experience by detecting fraud attempts at the point of impact and alerting both your security team and end users of these cybersecurity risks in real-time, at every stage of the customer journey.
Our watermark and alerts feature gives customers instant confidence that your websites and correspondence are legitimate without disrupting the customer experience. Our vision is a digital world where businesses can empower users to engage with digital assets, transact, and communicate online in complete confidence, without fear.
Want to learn more about how your customers and employees can ensure your sites and communication are legitimate? Check out our solution here.

Eran Tsur is CEO of Memcyco. He writes about the growing impact of digital impersonation, phishing, and account takeover attacks on global enterprises. His insights focus on how organizations can move beyond traditional fraud detection and adopt earlier detection strategies to stop impersonation-driven attacks before customer accounts and brand trust are compromised.