Introduction
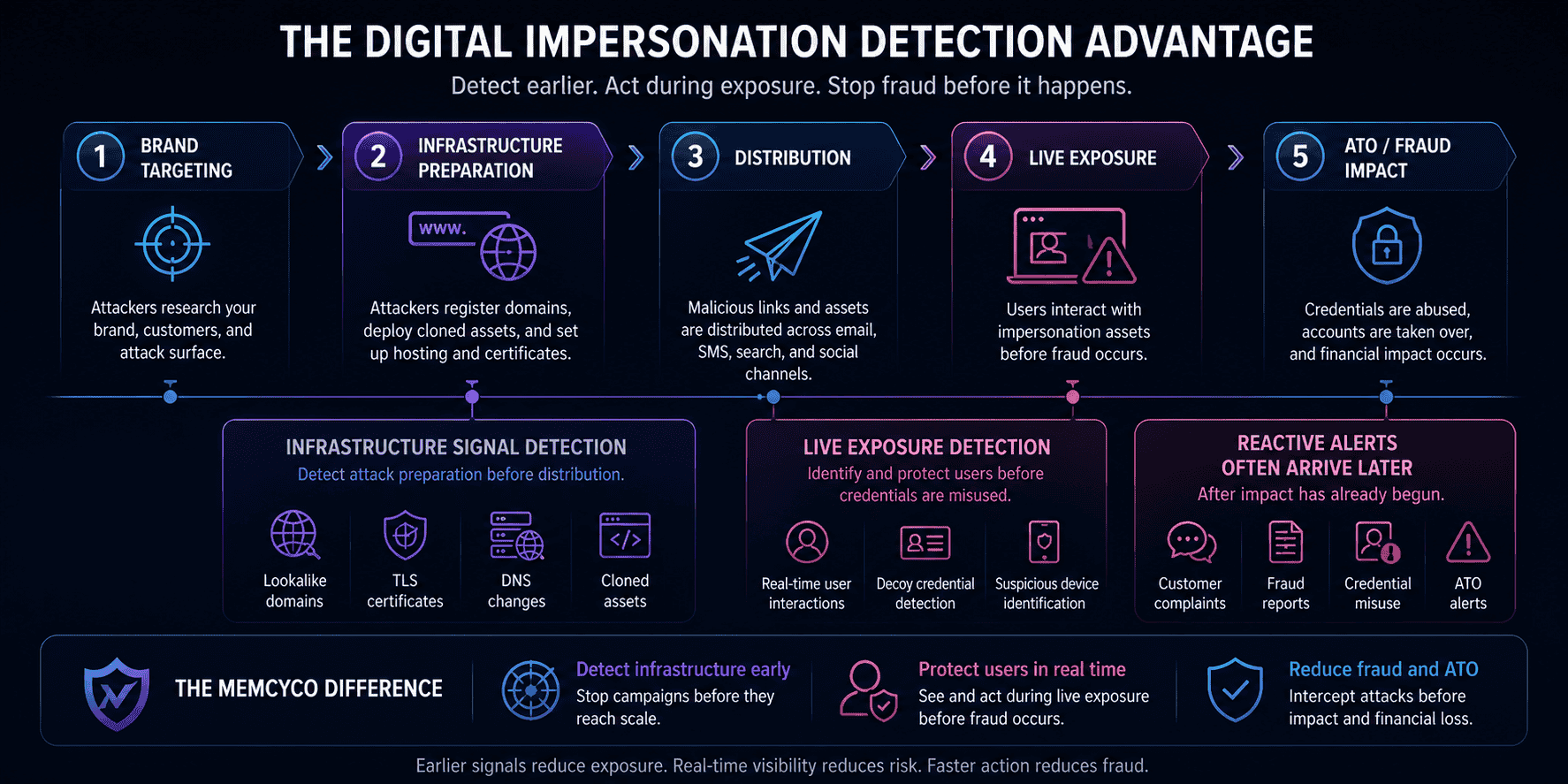
Phishing reports and customer complaints are not early warning signals. By the time they arrive, attackers have already built the infrastructure. Lookalike domains are live, credential harvesting pages are indexed, and the exposure window is open.
To stop digital impersonation attacks, organizations need to shift detection to the infrastructure preparation stage, before distribution begins. That means monitoring newly registered lookalike domains, detecting cloned brand assets, analyzing DNS and TLS signals, and executing rapid takedowns. DMARC is necessary but covers only one channel and one attack vector.
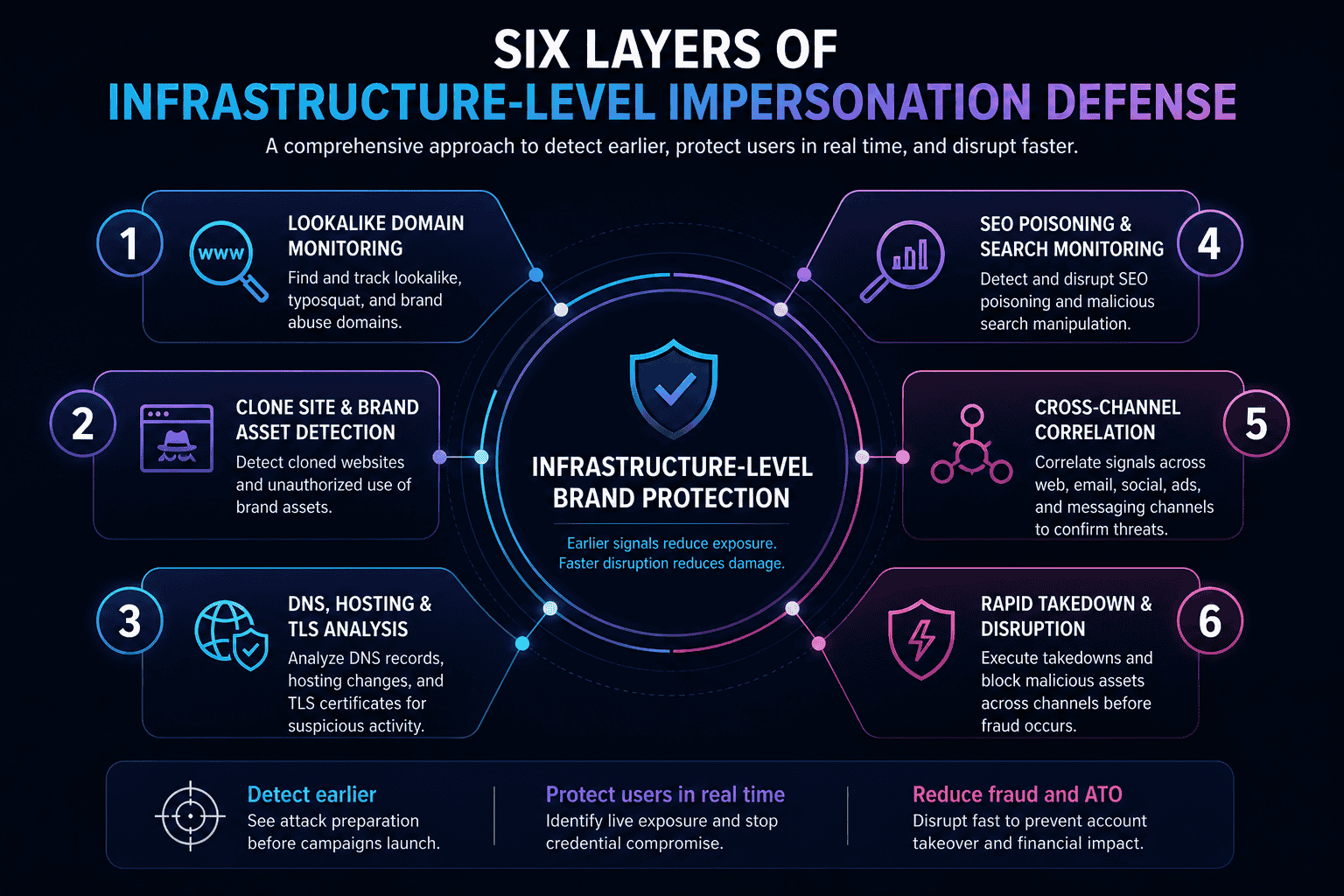
This guide covers a six-step framework for infrastructure-level impersonation defense, the attack lifecycle that makes early detection possible, and the operational metrics that tell you whether your program is actually working.
The Executive Briefing: Solving the Detection Timing Problem
- The DMARC Fallacy: Email authentication (DMARC/SPF/DKIM) only protects your exact domain. It has zero visibility into lookalike domains, cloned websites, smishing, or SEO poisoning, which attackers use to bypass your inbox controls entirely.
- The “Stage 2” Goal: Most defenses fire at Stage 4 (after victims are hit). To stop fraud, you must shift detection to Stage 2 (Infrastructure Preparation) by monitoring newly registered domains and TLS certificate transparency logs before the campaign even launches.
- Scam-as-a-Pipeline: Impersonation isn’t just a brand nuisance; it is a high-quality credential pipeline. Stolen credentials from cloned sites are “fresh” and bypass many traditional account takeover (ATO) controls that only look for leaked or recycled passwords.
- KPIs That Matter: Stop tracking takedown volume (a “vanity” metric). Instead, measure Detection Latency (time from site-live to detection) and Pre-Compromise Detection Rate to judge if your program is truly proactive.
Introduction: The Detection Timing Problem No One Is Talking About
Most enterprises believe they have impersonation covered. They’ve deployed DMARC. They have an email gateway. They have a SIEM. They don’t.
By the time any internal alert fires, whether from a fraud report, a customer complaint, or a security tool, attackers may already have active lookalike domains, cloned brand sites, and credential harvesting infrastructure running across email, SMS, paid search, and social media. The exposure window isn’t measured in hours. It’s measured in days.
This is the detection timing problem. And it’s costing enterprises far more than most security teams realize.
According to the FBI IC3 2024 Annual Report, phishing and spoofing was the #1 reported cybercrime by complaint volume in 2024, with 193,407 incidents. Total reported cybercrime losses reached $16.6 billion, a 33% increase from 2023. In November 2025, the FBI issued a PSA warning that ATO fraud via impersonation of financial institutions had caused over $262 million in losses since January 2025 alone.
Those numbers reflect what gets reported. The actual exposure is wider.
The security industry has conditioned organizations to treat digital impersonation as an inbox problem. It isn’t. DMARC, SPF, and DKIM are necessary controls, but they address one layer of a multi-layer attack surface. They don’t see lookalike domains. They don’t detect cloned sites. They don’t catch smishing campaigns or fraudulent paid search ads.
Impersonation is a lifecycle problem. Stopping it requires detecting attacker infrastructure before victims interact with it, not after fraud losses confirm the campaign was real.
This article gives security and fraud leaders a framework to do exactly that.
Why Most Impersonation Defense Happens Too Late
Most organizations don’t know they’re being impersonated until a customer calls to complain.
That’s not a process failure. It’s a structural one. The three most common detection triggers, a customer complaint, a fraud incident report, or a scheduled brand monitoring sweep, all fire after the attack infrastructure is already live. Victims may already be handing over credentials to a cloned site before a single internal alert fires.
This is the core timing problem. And it’s getting worse.
Attackers no longer need days to stand up impersonation infrastructure. Whalebone’s 2026 threat intelligence research confirms that the window between domain registration and an active phishing campaign has collapsed to hours. According to data cited by the Anti-Phishing Working Group (APWG), 41% of phishing domains are weaponized within 14 days of registration, many within the first 24 hours. By the time a lookalike domain surfaces in a brand monitoring report, it may already have harvested hundreds of credentials.
Email authentication controls, DMARC, SPF, and DKIM, are a necessary part of the defense stack. They do exactly what they’re designed to do: prevent attackers from spoofing your authenticated sending domains in email. That’s a real and valuable control.
But it’s one layer of a multi-layer problem.
DMARC has no visibility into lookalike domains (think paypa1.com vs. paypal.com). It doesn’t detect cloned websites, fraudulent social profiles, SMS-based smishing campaigns, or impersonation ads running in paid search. Attackers who register a fresh domain and clone your login page bypass email authentication entirely. They’re not spoofing your domain. They’re impersonating your brand from infrastructure you don’t control and can’t see.
The attack surface has expanded well beyond the inbox. Yet most detection programs are still anchored there.
Inbox controls are necessary. They’re just not sufficient, and the layers they don’t cover are precisely where modern impersonation campaigns operate.
What Email Authentication Actually Covers (And What It Doesn’t)
DMARC, SPF, and DKIM are doing exactly what they were designed to do. The problem is that attackers have moved well beyond what those designs anticipated.
Here’s what these controls actually cover:
- SPF specifies which mail servers are authorized to send email on behalf of your domain
- DKIM applies a cryptographic signature to verify that message content hasn’t been tampered with in transit
- DMARC ties both together, enforcing policy on emails that fail authentication and providing reporting visibility into who’s sending on your behalf
Together, they prevent attackers from spoofing your exact domain in email. That’s a meaningful control. But it’s one layer of a much larger attack surface.
Here’s what they don’t cover:
- Lookalike domains – a domain like `paypa1.com` or `paypal-secure.com` is attacker-owned infrastructure. It passes authentication checks because it’s not your domain. As Proofpoint noted in March 2026, “because lookalike domains are attacker-owned, they bypass authentication controls like SPF, DKIM, and DMARC entirely.”
- Cloned websites hosted on fraudulent domains – no email authentication protocol touches web infrastructure
- SMS-based smishing campaigns – outside email’s scope entirely
- Fraudulent paid search ads impersonating your brand in search results
- Social media impersonation profiles mimicking your brand or executives
On that last point, Cisco’s March 2026 blog put it plainly: social media impersonation “sits outside the scope of most existing security tooling.”
Email authentication isn’t obsolete. It solves one layer of a multi-layer problem. Treating DMARC enforcement as a complete impersonation defense leaves significant attack surface unmonitored and undefended.
The Digital Impersonation Attack Lifecycle: A Five-Stage Model
- Scope note: This model applies to external brand abuse campaigns targeting customer-facing assets. It does not cover insider threats, credential stuffing without impersonation, or all business email compromise variants.
Most impersonation defenses are built around the moment of delivery. That’s the wrong place to start. Understanding the full attack lifecycle reveals why detection timing is the most critical variable in reducing fraud exposure.
- Stage 1: Brand target selection
Attackers don’t pick targets randomly. They identify brands where customer trust is high, transaction volume is significant, and credential value is clear. According to the Anti-Phishing Working Group (APWG), financial institutions were the most-targeted sector in Q2 2025, accounting for 18.3% of all phishing attacks. Financial services, eCommerce, airlines, hospitality, and telcos are disproportionately targeted because their customers interact frequently and hold accounts worth compromising.
- Stage 2: Infrastructure preparation
This is where the attack is built, entirely outside your perimeter. Attackers register lookalike domains using typosquats, homoglyph substitutions, and combo-squats. They deploy cloned website content, replicate brand UI, and create fraudulent social profiles. No campaign has launched yet. No alert has fired. But the infrastructure is live.
- Stage 3: Multi-channel distribution
Attack infrastructure is activated across email, SMS, paid search, and social media, simultaneously or in sequence. Distribution is designed to maximize victim reach before any detection mechanism responds. By this stage, the exposure window is already open.
- Stage 4: Victim interaction and credential harvesting
Victims land on fraudulent assets and enter credentials, payment data, or personal information. This is the stage most organizations detect, after harm has already begun. Customer complaints, fraud reports, and inbox-level flags arrive here. It’s reactive by definition.
- Stage 5: Account takeover and fraud
Harvested credentials access legitimate accounts. Financial fraud, unauthorized transactions, and chargeback losses follow. The cost of the campaign is already accumulating.
Detection at Stage 2 versus Stage 4 is the difference between prevention and remediation. Organizations that monitor impersonation infrastructure before distribution begins shrink the exposure window to hours, not weeks. Those that wait for customer complaints are always cleaning up after the fact.
APWG recorded 3.8 million phishing attacks in 2025, and attackers have automated much of the infrastructure preparation process. The window between domain registration and campaign launch is narrowing. Waiting for Stage 4 signals isn’t a strategy. It’s a concession.
Stage 1–2: How Attackers Build Impersonation Infrastructure Before You Know It
By the time your security team gets its first alert, the attack may already be two weeks old.
Lookalike domain registration is typically the earliest observable signal of an impersonation campaign, and it happens long before any phishing email is sent or any victim is targeted. Attackers aren’t improvising. They’re building.
The domain manipulation playbook is well-established:
- Typosquatting – swapping or dropping letters to create near-identical domains (e.g., `paypa1.com` instead of `paypal.com`)
- Homoglyph attacks – substituting Latin characters with visually identical Unicode equivalents that are indistinguishable at a glance
- Combo-squatting – appending brand-adjacent words like `secure`, `login`, or `support` to create domains that feel legitimate (e.g., `yourbank-secure-login.com`)
- Subdomain abuse – embedding a real brand name as a subdomain of an attacker-controlled domain to pass casual inspection
In sophisticated campaigns, cloned website deployment follows domain registration within 24 to 72 hours. The site goes up. The TLS certificate gets issued, publicly logged in certificate transparency records that anyone can query. DNS records are configured. A hosting provider is selected.
Every one of these steps leaves an observable infrastructure signal before a single victim is touched.
APWG’s Q1 2025 Phishing Activity Trends Report recorded over one million phishing attacks in a single quarter, the highest volume since late 2023. Most of that infrastructure was registered and staged in advance. The exposure window opens at registration, not at delivery. If your monitoring starts at the inbox, you’re already behind.
Stage 3–5: Distribution, Harvesting, and the Downstream Fraud Chain
Attackers don’t pick one channel and hope for the best. They distribute simultaneously across email, SMS, paid search, and social media to maximize victim reach before any single channel’s defenses can respond.
This multi-channel approach exploits a real gap: detection latency varies sharply by channel. Email gateways may flag a phishing message within hours. A fraudulent paid search ad or fake social profile can persist for days, quietly harvesting credentials the entire time.
That asymmetry is deliberate. By the time one channel gets flagged, the others are still running.
Stage 4 is where damage becomes measurable. Victims enter credentials into cloned sites, convinced they’re on a legitimate page. Those credentials flow directly into Stage 5: account takeover and financial fraud. According to a November 2025 FBI IC3 PSA, ATO fraud via impersonation of financial institutions generated over $262 million in losses in 2025 alone. Equifax puts the broader consumer cost of ATO fraud at $15.6 billion in 2024.
The lifecycle doesn’t stall at credential theft. It accelerates. Every hour an impersonation campaign runs undetected is another hour the fraud chain compounds.
6 Proven Ways to Stop Digital Impersonation Attacks
These strategies assume DMARC, SPF, and DKIM are already deployed on your legitimate sending domains. They address the attack surface email authentication leaves uncovered, and they compound in effectiveness when implemented together.
Infrastructure-level impersonation defense requires layered monitoring across domains, cloned assets, DNS and TLS signals, search, messaging, social, and takedown workflows.
- 1. Monitor newly registered lookalike domains. Track typosquats, homoglyph variants, and brand-mimicking registrations as early infrastructure signals. Cisco identified over 30,000 lookalike domains targeting major brands in 2024 alone.
- 2. Detect cloned brand assets and visual impersonation. Identify copied logos, UI elements, and page content deployed on fraudulent domains before victims reach them.
- 3. Analyze DNS, hosting, and TLS infrastructure signals. Shared hosting clusters, recently issued certificates, and suspicious registrar patterns signal campaign preparation. Not definitive proof, but critical early context.
- 4. Detect SEO poisoning and search-based impersonation. Monitor branded queries for fraudulent pages in organic results or paid ads. The FBI’s IC3 flagged SEO poisoning as an active tactic used to impersonate financial institutions.
- 5. Correlate impersonation indicators across channels. Connect signals from email, SMS, search, and social into a unified threat picture. APWG recorded 3.8 million phishing attacks in 2025, with SMS-based threats rising in Q4.
- 6. Implement rapid takedown and disruption workflows. Reducing time between detection and infrastructure removal directly shrinks the active exposure window. Speed of disruption is the metric that matters most.
Step 1: Monitor Newly Registered Lookalike Domains
Domain registration is where most impersonation campaigns leave their first footprint, often visible days before any phishing message is sent.
Monitoring newly registered domains gives security teams a shot at detecting campaigns at Stage 2 of the attack lifecycle, before distribution begins. What to watch for:
- Typosquats – character substitutions, transpositions, or omissions (e.g., `paypa1.com`)
- Homoglyph variants – visually similar Unicode characters replacing standard letters
- Combo-squats – brand name combined with high-risk terms like `login`, `secure`, `verify`, or `support`
- Brand-plus-TLD abuse – legitimate brand names registered under new or obscure top-level domains
Continuous monitoring draws on certificate transparency logs, WHOIS registration feeds, and passive DNS records. A Google Threat Intelligence adoption guide states that “continuous, automated monitoring of newly registered domains, DNS changes, and certificate issuances for brand look-alikes is not merely a best practice. It’s a necessity.”
Not every lookalike domain is malicious. Brands defensively register many themselves. Effective monitoring applies risk scoring based on supporting signals: hosting provider reputation, TLS certificate issuance timing, and DNS configuration patterns.
The common mistake is treating domain monitoring as a periodic audit. By the time a quarterly review runs, active campaigns may already be harvesting credentials.
Step 2: Detect Cloned Brand Assets and Visual Impersonation
Registering a lookalike domain is step one. Deploying a convincing replica of your website is step two. That’s where credential harvesting actually happens.
Attackers clone legitimate brand sites with precision: copying HTML structure, CSS styling, logos, login forms, and even legal copy to create pages that are visually indistinguishable from the real thing. APWG data shows that over 55% of phishing sites actively impersonate real brands, and AI-assisted tools are accelerating the cloning process significantly.
Visual impersonation detection scans the web for pages reproducing your brand’s identity without authorization. It looks for:
- Copied page structure and UI elements
- Unauthorized use of brand logos and trademarks
- Cloned login forms designed to harvest credentials
- Pixel-for-pixel reproductions of product or checkout pages
This detection layer is distinct from domain monitoring. A cloned site can sit on a lookalike domain or on a completely unrelated domain with no obvious connection to your brand.
The operational value is timing. Detecting a cloned site before it receives significant traffic creates a takedown window before harvesting begins. Waiting for customer reports is the common mistake. By the time a victim flags a fake page, credentials are already compromised.
Step 3: Analyze DNS, Hosting, and TLS Infrastructure Signals
Infrastructure signals don’t confirm an attack is live. They tell you one is being built.
When attackers prepare an impersonation campaign, they leave fingerprints across DNS, hosting, and TLS certificate records before a single phishing message is sent. Monitoring these signals gives security teams an earlier warning than waiting for victim reports.
Key signals worth tracking:
- TLS certificate issuance for lookalike domains, visible via public certificate transparency logs. SANS ISC captures roughly 250,000 new domains daily using this method, flagging suspicious registrations before they go active.
- Hosting on bulletproof or high-abuse providers, which routinely disregard takedown requests and are disproportionately associated with phishing infrastructure.
- DNS records pointing to known malicious IP ranges, or rapid DNS changes consistent with fast flux techniques. CISA has classified fast flux as a national security threat, noting it lets attackers rotate IP addresses faster than defenders can block them.
The critical mistake is treating these signals as binary proof. They’re probabilistic risk indicators, not standalone takedown triggers.
Infrastructure analysis becomes genuinely powerful when combined with domain monitoring and visual clone detection. When multiple signals converge, a lookalike domain, a freshly issued TLS certificate, and hosting on a known abuse provider, confidence that a campaign is in preparation rises significantly.
Step 4: Detect SEO Poisoning and Search-Based Impersonation
Search is a blindspot most security teams don’t protect. Attackers know it.
SEO poisoning is a distinct impersonation vector: attackers optimize fraudulent pages to rank for branded search queries, or buy paid ads that impersonate your brand, routing high-intent users directly to credential harvesting infrastructure. What makes this dangerous isn’t technical sophistication. It’s the trust dynamic. A user who searches for your brand and clicks a top result initiated that interaction. Their guard is down.
Microsoft’s Security Blog documented a 2026 campaign where threat actor Storm-2561 pushed fake VPN software pages to the top of search results, harvesting enterprise credentials from users who believed they were downloading legitimate software. The attack chain started with a search query.
Malvertising compounds the problem. According to The Media Trust via Cybersecurity Insiders, nearly 60% of malware and phishing incidents in 2025 were linked to online ads. Fraudulent paid search ads appear and vanish within hours, making point-in-time scans useless.
Detection requires continuous SERP monitoring: tracking branded queries for fraudulent organic rankings, flagging unauthorized brand use in paid ads, and identifying pages that visually mimic your brand on attacker-controlled domains.
Memcyco includes SEO poisoning detection and disruption as a core capability, identifying search-based impersonation before significant victim traffic accumulates. Don’t assume email phishing is the higher-risk vector. When users arrive via search, conversion rates on fraudulent pages are often higher, because the user came looking.
Step 5: Correlate Impersonation Indicators Across Channels
Attackers don’t pick one channel and commit. They spread across all of them at once.
A coordinated impersonation campaign typically runs a lookalike domain, a cloned site, a fraudulent social profile, and an SMS distribution chain as a single operation. If your domain monitoring team, social media team, and email security team each see one piece of that picture in isolation, no one sees the campaign. According to the APWG Phishing Activity Trends Report Q3 2025, social media already accounts for 14.6% of phishing attacks, making it the second-largest attack channel after web-based phishing. That’s not a secondary signal. It’s a primary one.
Cross-channel correlation changes the operational picture in three concrete ways:
- Faster campaign attribution: Connecting a newly registered domain to a fraudulent social profile and an SMS blast confirms a coordinated campaign, not an isolated incident.
- More accurate threat classification: Multi-channel evidence distinguishes active fraud infrastructure from passive typosquatting, which sharpens prioritization.
- Stronger takedown cases: Registrars, hosting providers, and social platforms respond faster when you can demonstrate coordinated abuse across multiple channels, not just a single suspicious URL.
The most common failure mode here isn’t a technology gap. It’s a workflow gap. Domain monitoring, social monitoring, and email security operate in separate silos with no structured correlation process. Each team files its own reports. No one connects the dots. The campaign persists longer than it should.
Cross-channel correlation requires either a unified monitoring platform or a formal data-sharing workflow between security, fraud, and brand protection teams. Without one, detection latency compounds across every channel the attacker uses.
Step 6: Implement Rapid Takedown and Disruption Workflows
Detection without disruption is just expensive surveillance.
The gap between identifying an active impersonation asset and removing it is your real exposure window. Call it disruption velocity. It’s one of the most consequential operational metrics in your program, and most teams don’t track it.
Effective takedown workflows aren’t improvised. They require:
- Pre-established relationships with domain registrars, hosting providers, and platform trust and safety teams
- Standardized abuse report templates with evidence packages ready to submit, not assembled under pressure
- Escalation paths for high-urgency campaigns, particularly those actively harvesting credentials
- Status tracking for every open takedown request, with resolution time logged
Be realistic about timelines. Registrar domain removal can take 48-72 hours under standard conditions, and CAIDA research found that phishing domains stay accessible for an average of 11.5 days after detection. That’s a long time for a cloned site to stay live.
This is why disruption can’t wait for takedown to complete. Blocking malicious domains at the DNS or network layer, submitting URLs to browser safe browsing lists, and alerting affected customers are all actions you can take while the formal takedown process runs.
Memcyco’s Takedown Services operationalize this entire workflow. One CISO at a top-10 North American bank reported that incident handling times dropped from 72 hours to under one hour after deployment.
One final mistake to avoid: treating takedown as the end of the response. Sophisticated attackers re-register similar domains or redeploy infrastructure within hours of removal. Your program needs to track reactivation, not just resolution.
Prerequisites: What You Need Before Implementing This Framework
Jumping into external monitoring without the right foundations generates noise, not signal. Before operationalizing the six strategies below, confirm these five prerequisites are in place.
- 1. Email authentication baseline
DMARC, SPF, and DKIM must be deployed and enforced across all legitimate sending domains. This closes the exact-domain spoofing gap before you expand detection scope outward. Without enforcement, you’re chasing external threats while your own domains stay exposed.
- 2. Brand asset inventory
Document every legitimate domain, subdomain, social profile, mobile app, and visual asset your brand owns. This is the baseline against which impersonation is measured. You can’t detect a fake without a clear picture of the real.
- 3. Cross-functional alignment
Impersonation defense spans security, fraud prevention, legal, and customer experience teams. Define ownership and escalation paths before monitoring generates alerts. Alerts without clear owners become noise.
- 4. Takedown authority and relationships
Legal authority to submit takedown requests, combined with pre-established contacts at key registrars and platforms, directly cuts disruption time. Relationships built before an incident move faster than cold outreach during one.
- 5. Monitoring tooling or managed service
Continuous coverage across domain registration feeds, web content, search results, and social platforms requires dedicated tooling or an external service. Manual spot-checks won’t scale.
Organizations missing these foundations will struggle to operationalize the six strategies at any meaningful scale.
How Digital Impersonation Connects to Account Takeover and Fraud Losses
Impersonation campaigns don’t end when a victim clicks away from a cloned site. That’s where the real damage begins.
The chain is direct: a victim enters credentials on a fraudulent lookalike page, believing it’s legitimate. The attacker captures those credentials in real time and attempts login on the genuine platform. A successful account takeover then enables unauthorized transfers, account draining, and fraudulent purchases, often within minutes. This is digital impersonation operating as a credential pipeline, not just a brand nuisance.
What makes impersonation-harvested credentials particularly dangerous is their freshness. Unlike credential stuffing attacks, which recycle previously breached lists, credentials stolen through active impersonation campaigns are new. They haven’t been rotated. They haven’t surfaced in breach monitoring systems yet. By the time any alert fires, the attacker may already be inside the account.
The financial scale is significant. The FBI’s IC3 reported in November 2025 that ATO fraud via impersonation of financial institutions caused over $262 million in losses in 2025 alone, across more than 5,100 complaints. Separately, Equifax reported that ATO fraud consumer costs reached $15.6 billion in 2024, with ATO-related chargeback losses running 76% higher than typical chargebacks.
The business impact extends beyond direct fraud losses. Chargeback costs accumulate. Customers who experience account compromise churn at elevated rates. Javelin Strategy found that 42% of ATO victims closed the affected account entirely. Regulatory scrutiny follows. And the reputational damage from customers associating your brand with a scam they fell for is harder to quantify, but very real.
Detecting impersonation infrastructure earlier in the lifecycle directly reduces the volume of credentials harvested, and shrinks the downstream ATO exposure that follows.
Measuring Impersonation Disruption Effectiveness: Operational KPIs
Most impersonation programs track the wrong thing: takedown volume. That number tells you how busy your team is, not whether your program is working.
The five KPIs below give security and fraud leaders a directional framework for tracking program maturity over time. Baselines vary by industry, brand size, and existing tooling, so treat these as progress indicators, not fixed targets.
From Takedown Volume to Exposure Window Reduction
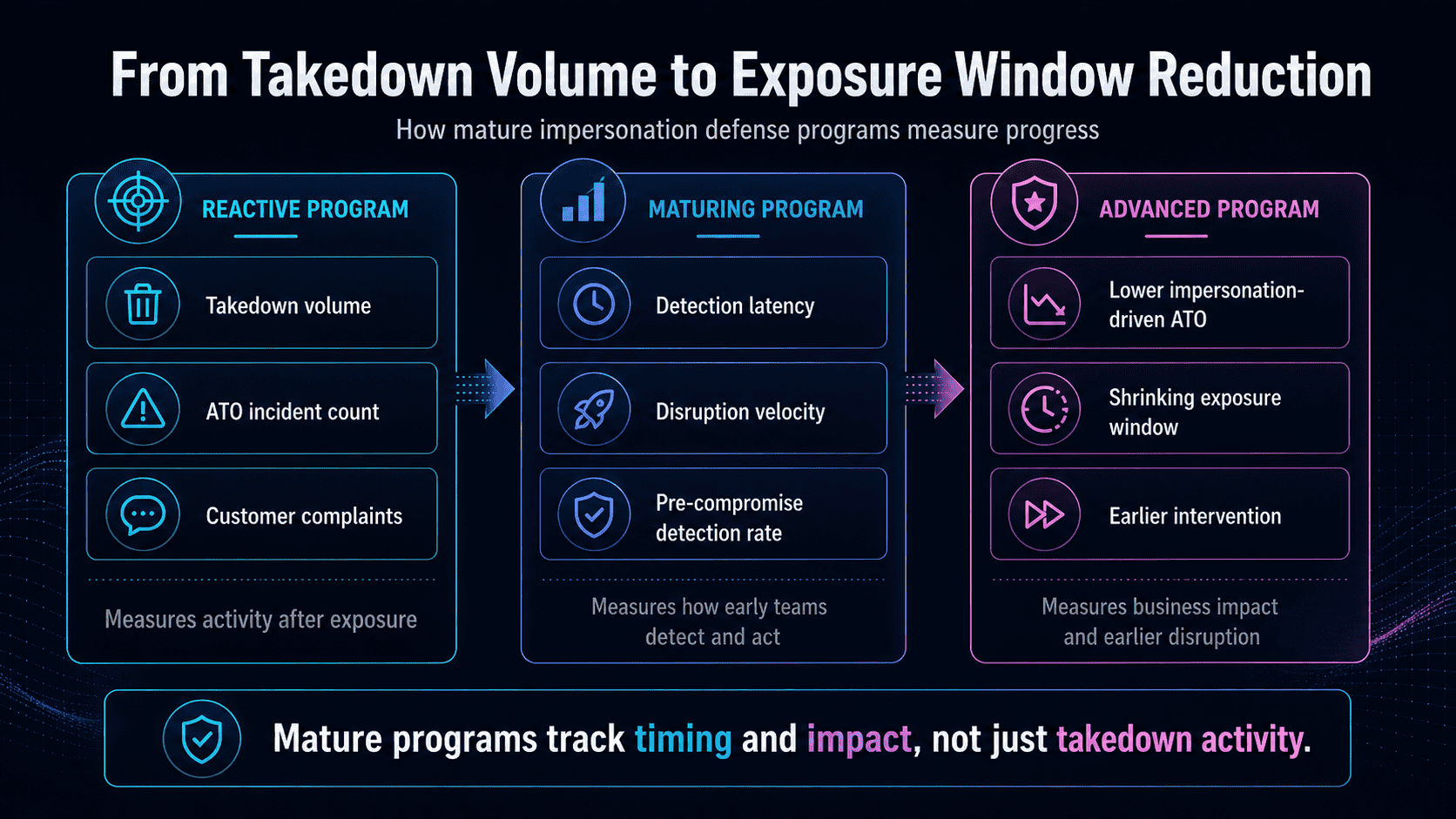
- KPI 1: Detection latency
Definition: Time between impersonation infrastructure activation (domain registration or site deployment) and internal detection.
Why it matters: Research published in 2025 found the average phishing site lifespan is just 54 hours. If your detection latency runs in days, you’re arriving after the damage is done. Directional goal: reduce over time as monitoring coverage matures.
- KPI 2: Disruption velocity
Definition: Time between detection and successful takedown or disruption of impersonation assets.
Why it matters: Detection without action is just awareness. Pre-established registrar relationships and standardized takedown workflows are the levers that compress this window. Directional goal: reduce through process maturity, not just tooling.
- KPI 3: Pre-compromise detection rate
Definition: Percentage of impersonation campaigns detected before credential harvesting begins, caught at infrastructure preparation or early distribution stages.
Why it matters: This is the most strategically significant KPI in the framework. It directly measures whether your program is shifting from reactive to proactive. A rising pre-compromise detection rate means you’re disrupting campaigns before victims are exposed. Directional goal: increase as infrastructure monitoring matures.
- KPI 4: Impersonation-driven ATO incident rate
Definition: Volume of account takeover incidents attributable to impersonation-sourced credential harvesting, tracked over time.
Why it matters: This connects upstream detection to downstream fraud losses. IBM’s 2025 Cost of a Data Breach Report found phishing was the most common initial attack vector, responsible for 16% of breaches at an average cost of $4.8 million per incident. Directional goal: decrease as pre-compromise detection improves. Memcyco customers have documented up to a 50% reduction in ATO incidents through infrastructure-level detection.
- KPI 5: Active impersonation asset count per campaign
Definition: Average number of domains, pages, and social profiles identified per detected campaign.
Why it matters: This is a campaign complexity indicator, not a success metric on its own. Rising asset counts signal attackers are investing more in redundancy, raising the bar for disruption velocity. Track it alongside KPIs 1 and 2 to assess whether takedown workflows are keeping pace.
Together, these five KPIs form a maturity arc: from reactive programs that count takedowns to proactive programs that measure how early they intervene. When KPI 3 replaces KPI 4 as your primary success metric, your program has crossed that threshold.
How to Verify Your Impersonation Defense Program Is Working
Here are six operational checkpoints that signal whether your impersonation defense program is maturing or stalling.
- Detection latency is trending downward. Track the time between when impersonation infrastructure goes live and when your team identifies it. Mandiant’s M-Trends 2026 report puts global median dwell time at 14 days in 2025. Your program should beat that benchmark and improve quarter-over-quarter.
- You’re catching campaigns at Stage 2, not Stage 4. If every detection traces back to a customer complaint or fraud alert, you’re operating reactively. A maturing program catches lookalike domain registrations and cloned site deployments before credential harvesting begins.
- Takedown requests go out within hours. Days-long gaps between detection and submission keep infrastructure active longer. Speed here directly shrinks the exposure window.
- Cross-channel signals produce unified campaign views. Siloed alerts from email, SMS, and social monitoring aren’t enough. If your team can’t connect those signals into a single campaign picture, correlation is broken.
- Impersonation-driven ATO is tracked as a distinct fraud category. Lumping it into general account takeover hides the trend line. Separate attribution enables accurate measurement of program impact.
- The program generates proactive intelligence. Newly registered lookalike domains appearing in your feed before any victim reports them is a strong maturity signal. Reactive-only programs don’t produce that.
These aren’t pass/fail criteria. They’re directional indicators. Progress on each one means your exposure window is shrinking.
Common Troubleshooting: Why Impersonation Programs Stall
Most impersonation defense programs don’t fail because of bad intent. They fail because of five structural problems that quietly erode effectiveness over time.
- Issue 1: Alert fatigue from domain monitoring
Domain monitoring tools generate high volumes of low-confidence alerts. Without risk scoring, analysts can’t separate real threats from noise. The 2025 Unit 42 Global Incident Response Report identified alert fatigue as a key enabler of successful social engineering attacks. Fix this by scoring alerts on corroborating signals: domain age, TLS issuance timing, hosting provider, and visual similarity to your brand. One signal is noise. Four signals together are a threat.
- Issue 2: Siloed monitoring with no correlation
Domain, social, and email monitoring teams often operate independently. Each sees a fragment of the attack. None sees the full picture. Establish a cross-channel correlation workflow, or adopt a unified platform that connects signals into a single threat view.
- Issue 3: Slow takedown response
Takedown requests stall when teams scramble to establish registrar relationships mid-incident. Build those relationships before an attack lands. Pre-negotiated contacts with registrars and hosting platforms cut response time from days to hours.
- Issue 4: No pre-compromise detection
If every detection occurs at Stage 4 or later, after distribution has already begun, the program is structurally reactive. Shift investment toward Stage 2 infrastructure monitoring: lookalike domain registration, hosting provisioning, and cloned asset deployment. That’s where the exposure window can actually be shortened.
- Issue 5: No impersonation attribution in ATO reporting
Account takeover incidents get logged, but the credential source rarely gets traced back to an impersonation campaign. Add impersonation attribution to fraud investigation workflows. Without it, you’re treating symptoms and missing the root cause entirely.
Next Steps: Building an Infrastructure-Level Brand Protection Program
By the time a customer complaint lands in your inbox, the exposure window is already open. Credentials may already be harvested. Fraud losses are already accumulating. Javelin Strategy & Research found that account takeover alone cost consumers nearly $16 billion in 2024, and the majority of that starts with impersonation infrastructure your current controls never saw.
If your program detects at Stage 4 instead of Stage 2, that gap is costing you.
Here are three concrete steps to close it.
- 1. Audit your current detection triggers
Map where in the impersonation lifecycle your program actually fires. Are you detecting at Stage 2, when lookalike domains are registered and clone sites go live? Or at Stage 4, after credentials are already being harvested? Quantify that gap. It’s the single most honest measure of your current exposure
- 2. Map your brand’s full impersonation attack surface
Document every channel where your brand can be impersonated: registered domains, social media profiles, paid search results, SMS, and mobile app stores. Then assess your monitoring coverage for each. Most organizations find significant blind spots outside email, channels where attackers operate freely and quietly.
- 3. Evaluate infrastructure-level monitoring capabilities
Ask whether your current tooling provides continuous domain registration monitoring, visual impersonation detection, cross-channel signal correlation, and rapid takedown workflows. If the answer is no on more than one, your detection model is structurally reactive.
The framework in this article reflects how modern impersonation campaigns actually operate, and where they can be disrupted before the damage is done.
For organizations ready to move from reactive detection to infrastructure-level brand protection, explore how Memcyco’s platform reduces impersonation-driven fraud exposure, including real-time clone site detection, lookalike domain monitoring, and account takeover prevention.
Frequently Asked Questions
- Does DMARC protect against lookalike domain attacks?
No. DMARC, SPF, and DKIM authenticate your legitimate sending domains and prevent attackers from spoofing your exact domain in email. But lookalike domains (e.g., paypa1.com, paypa1-secure.com) are attacker-owned infrastructure. DMARC has no authority over domains it doesn’t control, so these attacks bypass email authentication entirely. As Proofpoint confirmed in 2026, lookalike domains sidestep SPF, DKIM, and DMARC by design. Stopping them requires external domain monitoring, not inbox controls.
- How quickly can impersonation infrastructure cause damage?
Faster than most detection programs can respond. Research published in 2025 found the average phishing site lifespan is 54 hours, but the median is under six hours. Many campaigns harvest credentials and disappear before a takedown request is even filed. Attackers register domains, clone sites, and begin distributing phishing links within hours of campaign launch. The exposure window opens long before customer complaints surface.
- Is impersonation only an email problem?
Not even close. Modern impersonation campaigns run across email, SMS, paid search ads, and social media simultaneously. APWG documented SMS-based smishing increasing by nearly 35% in Q3 2025 alone. Attackers use whichever channel reaches victims fastest and switch channels mid-campaign to evade single-vector detection. Effective defense requires cross-channel visibility, not just email monitoring.
- How does impersonation connect to account takeover fraud?
Directly. Credentials harvested from cloned brand sites feed straight into account takeover attempts. Veriff’s Fraud Report 2026 found that impersonation fraud accounted for over 85% of all fraud attempts in 2025, with the net fraud rate across digital verification flows remaining above 4%. Once attackers have valid credentials, they move fast: changing contact details, initiating transfers, and locking out legitimate users before fraud teams detect the breach.
- What’s the difference between brand monitoring and impersonation infrastructure detection?
Brand monitoring tracks mentions, sentiment, and trademark misuse after the fact. Impersonation infrastructure detection focuses on the attack preparation layer: newly registered lookalike domains, cloned site deployments, DNS and TLS signals, and fraudulent social profiles, before campaigns reach victims. The distinction matters operationally. Brand monitoring tells you your name is being misused. Infrastructure detection tells you a campaign is being built, giving security teams a window to disrupt it before credential harvesting begins.
Conclusion
Stopping digital impersonation attacks requires moving detection upstream. Email authentication handles spoofing on your legitimate domains. It does nothing for lookalike domains, cloned sites, or search-based impersonation. The six-step framework in this guide addresses the full attack surface, from infrastructure registration through takedown, giving security and fraud teams a realistic path from reactive detection to pre-compromise disruption.
Go from Reactive Detection to Infrastructure-Level Brand Protection, with Memcyco
If impersonation detection begins only after customer complaints arrive, the exposure window is already open. Learn how infrastructure-level brand monitoring reduces impersonation-driven fraud exposure before credentials are harvested.
Explore Infrastructure-Level Brand Protection
Or schedule a product demo to learn more about how Memcyco changes the way scam-targeted enterprises fight account takeover, and other digital fraud.
FAQs
Q: Does DMARC protect against lookalike domain attacks?
A: No. DMARC, SPF, and DKIM authenticate email sent from your legitimate domains – they verify that messages claiming to originate from your domain are actually sent by authorized infrastructure. Lookalike domains (e.g., paypa1.com, paypal-secure.com) are attacker-owned domains that bypass authentication controls entirely because they are not your domain. DMARC enforcement on your legitimate domain does not prevent attackers from registering visually similar domains and sending phishing emails from them. Protecting against lookalike domain attacks requires continuous monitoring of newly registered domains that mimic your brand, combined with rapid takedown workflows.
Q: How early in an impersonation campaign can organizations realistically detect the threat?
A: With infrastructure-level monitoring, detection can occur at Stage 2 of the attack lifecycle – during infrastructure preparation, when attackers register lookalike domains and deploy cloned sites, before any phishing distribution begins. Domain registration data, certificate transparency logs, and passive DNS feeds provide signals that are observable days or weeks before a campaign reaches victims. Without infrastructure monitoring, most organizations detect impersonation at Stage 4 – after victims have already interacted with fraudulent assets and credentials may already be harvested. The gap between Stage 2 and Stage 4 detection represents the difference between prevention and remediation.
Q: What is the difference between brand protection and impersonation attack prevention?
A: Traditional brand protection focuses on trademark enforcement – identifying unauthorized use of brand assets and pursuing legal remediation. Impersonation attack prevention is a security and fraud discipline focused on detecting and disrupting active threat infrastructure before it causes credential harvesting and financial fraud. The two disciplines overlap but are not identical: brand protection addresses a broader range of brand abuse (counterfeit goods, trademark infringement), while impersonation attack prevention is specifically focused on the attack lifecycle that leads to account takeover and fraud losses. Effective enterprise programs integrate both, with security and fraud teams owning the threat detection and disruption workflow.
Q: How does impersonation-driven credential harvesting differ from credential stuffing?
A: Credential stuffing uses previously breached credential lists – typically purchased on dark web markets – to attempt account logins at scale. Impersonation-driven credential harvesting actively deceives victims into voluntarily entering their credentials on fraudulent sites that mimic legitimate brands. The key operational difference: impersonation-harvested credentials are fresh (not yet rotated or flagged in breach monitoring systems), often belong to active users with high account value, and are not yet present in breach databases that credential monitoring services scan. This makes impersonation-harvested credentials particularly dangerous for account takeover – they bypass many of the controls designed to detect stuffing attacks.
Q: What metrics should security leaders use to measure impersonation defense program effectiveness?
A: The most strategically significant metric is pre-compromise detection rate: the percentage of impersonation campaigns detected before credential harvesting begins. This directly measures whether your program is operating proactively (Stage 2 detection) or reactively (Stage 4 detection). Supporting metrics include detection latency (time from infrastructure activation to internal detection), disruption velocity (time from detection to successful takedown), and impersonation-driven ATO incident rate (volume of account takeover incidents attributable to impersonation-sourced credentials, tracked over time). These metrics should be tracked as directional indicators of program maturity – baseline performance varies by industry and brand size, and improvement trends matter more than absolute values.
Q: Can impersonation attacks be fully prevented?
A: No, and any vendor or framework claiming universal prevention should be viewed skeptically. Attackers can register new domains, deploy new infrastructure, and launch new campaigns faster than any detection system can guarantee pre-distribution interception for every campaign. The realistic goal of an impersonation defense program is to reduce the exposure window: detect more campaigns earlier in the lifecycle, disrupt infrastructure faster after detection, and reduce the volume of victims who interact with fraudulent assets before takedown. Programs that shift from Stage 4 detection to Stage 2 detection meaningfully reduce fraud losses even without achieving complete prevention.