Phishing remains one of the most one of the most common initial access techniques used in major breaches, according to the Verizon Data Breach Investigations Report 2025.
At the same time, the rise of phishing-as-a-service (PhaaS) platforms has industrialized social engineering. Criminal marketplaces now offer ready-made phishing kits with templates, infrastructure, and automation tools that allow attackers to launch sophisticated campaigns with minimal technical expertise.
Many modern phishing kits also use adversary-in-the-middle (AitM) techniques, which capture authentication tokens and session cookies in real time to bypass traditional multi-factor authentication protections.
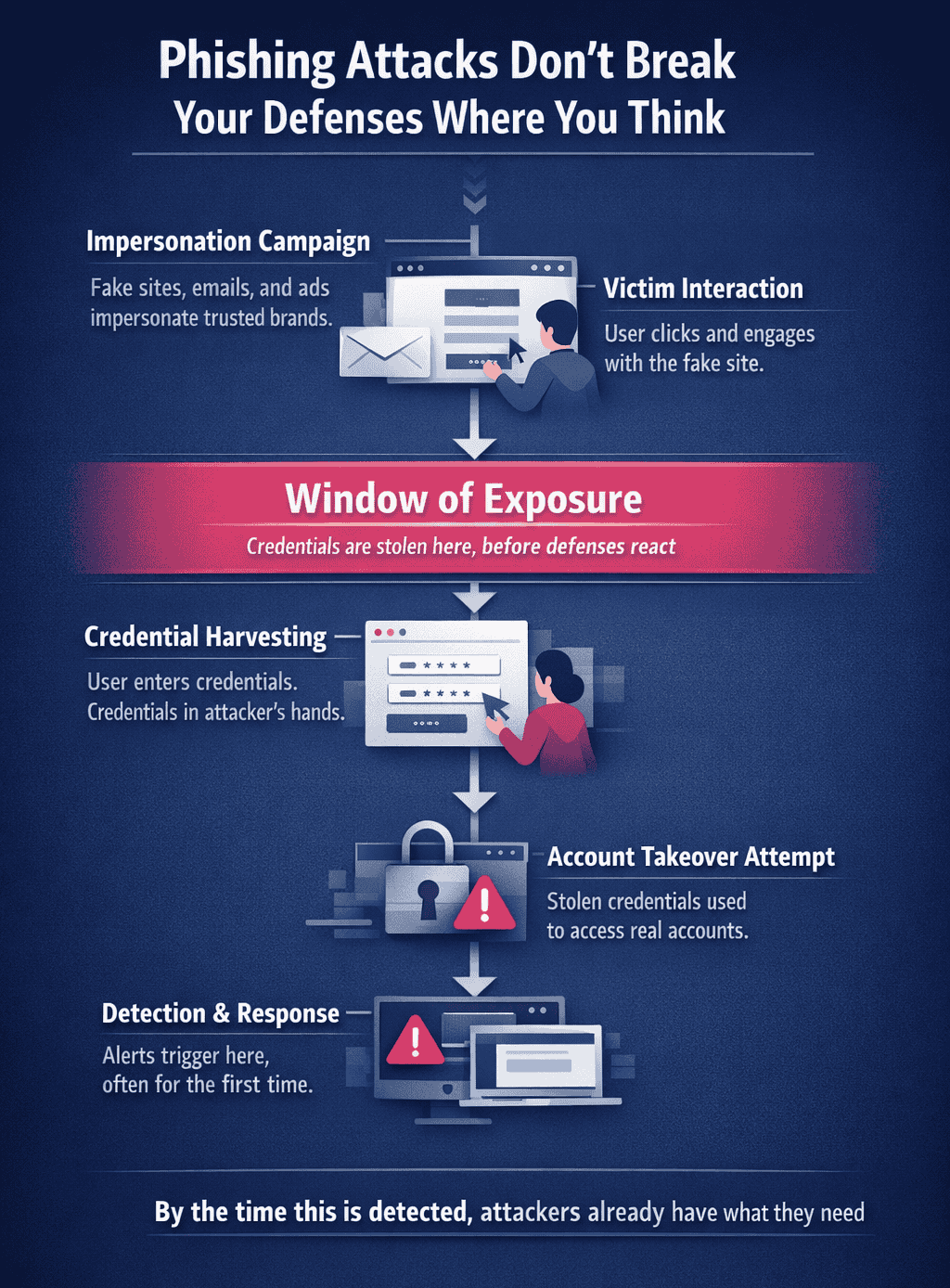
Phishing attacks no longer follow a single path with modern attacks commonly converging on identity from multiple vectors.
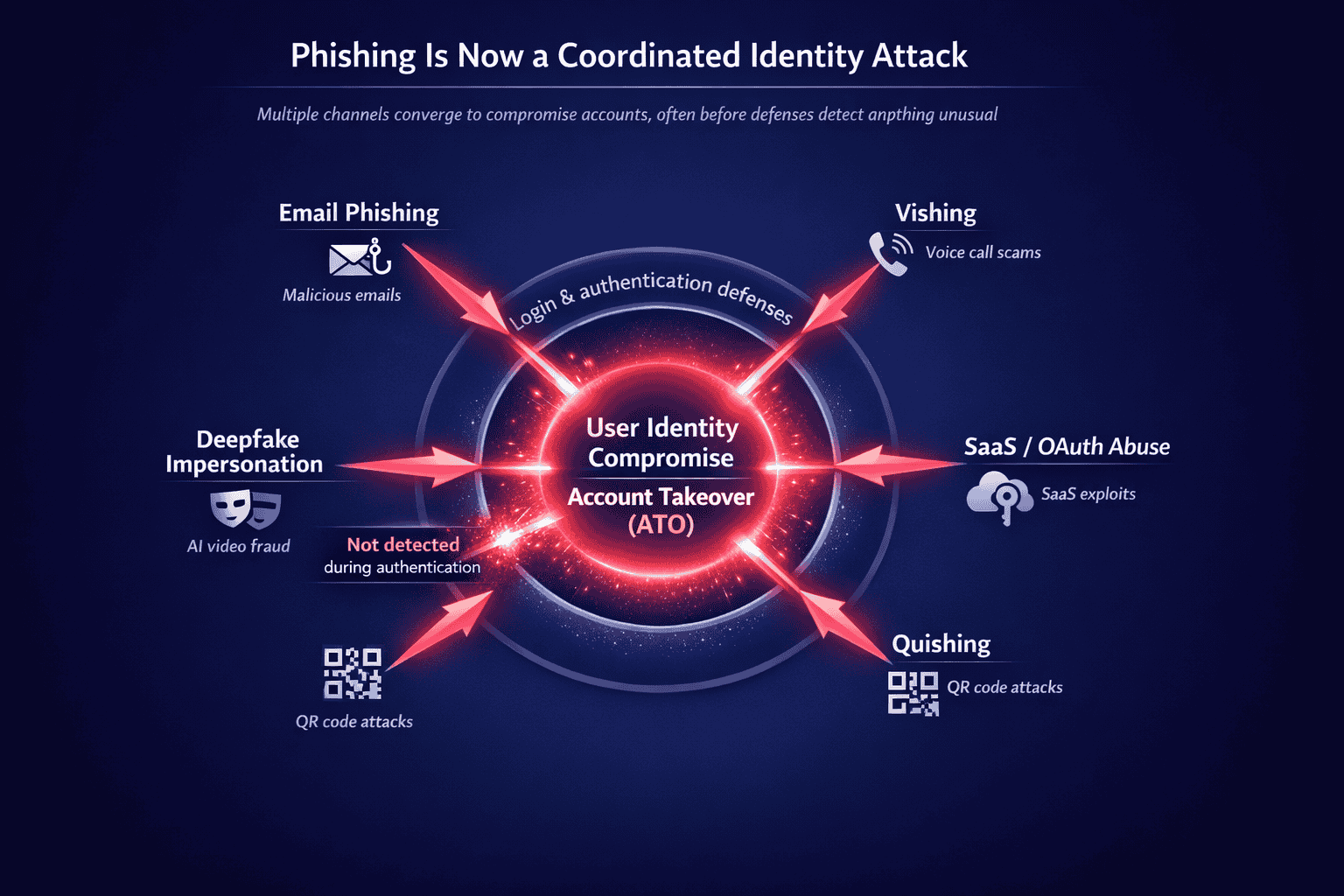
Across these attack paths, the critical moment is the same: activity that appears legitimate passes through authentication without raising suspicion.
The following case studies highlight five real-world phishing attack examples from 2025 and what security teams can learn from them.
1. Conduent Backend Breach
In early 2025, global business services provider Conduent disclosed a breach that exposed sensitive personal information belonging to millions of individuals across the United States, according to reporting from BleepingComputer.
[LINK: BleepingComputer – Conduent breach]
Investigators determined that attackers initially gained access by compromising VPN credentials, which are commonly obtained through phishing campaigns or credential harvesting operations. Once inside the network, the threat group moved laterally through Conduent’s infrastructure and ultimately exfiltrated 8.5 terabytes of sensitive data, including Social Security numbers and healthcare information.
Because Conduent processes data for government agencies and healthcare organizations, the breach had a cascading impact across multiple sectors.
What this attack revealed
Service providers that process sensitive data for multiple organizations represent high-value targets for credential-based phishing campaigns.
Lesson for security teams
Protect vendor access and administrative credentials with strong authentication controls and monitoring for suspicious login behavior.
2. The Aflac Vishing Campaign
In 2025, insurance provider Aflac disclosed a breach affecting over 22 million individuals, linked to a sophisticated voice phishing campaign, according to SecurityWeek.
The attack was attributed to the threat group Scattered Spider, known for its advanced social engineering tactics. Rather than relying on traditional phishing emails, attackers called IT support staff while impersonating legitimate employees.
During these calls, the attackers convinced support personnel to reset credentials or transfer multi-factor authentication to attacker-controlled devices. By exploiting help desk processes and impersonating internal staff, the group gained legitimate access to corporate systems.
The incident was part of a broader campaign targeting the insurance industry.
What this attack revealed
Identity support teams and help desks remain one of the most effective social engineering targets for attackers.
Lesson for security teams
Require strict identity verification and secondary approval before resetting credentials or transferring MFA devices.
3. The Salesforce SaaS Authorization Exploitation
In mid-2025, researchers uncovered a campaign targeting Salesforce environments at multinational organizations including Google, Adidas, Chanel, and Qantas, according to reporting from Malwarebytes.
The attacks were attributed to the cybercriminal group ShinyHunters, which used social engineering to trick employees into authorizing malicious applications within Salesforce.
Attackers contacted employees while posing as internal IT staff and instructed them to connect a “security update” tool to Salesforce. In reality, the tool was a malicious version of a legitimate integration that granted attackers persistent OAuth API access to corporate CRM environments.
Because OAuth tokens provide long-term access, attackers were able to extract sensitive corporate data without needing passwords or bypassing MFA.
What this attack revealed
Modern phishing campaigns increasingly exploit SaaS integrations and authorization workflows rather than stealing passwords directly.
Lesson for security teams
Audit OAuth application permissions and restrict which third-party tools can request access to enterprise SaaS platforms.
4. The Arup Deepfake Financial Fraud
One of the most widely reported phishing incidents of 2025 involved engineering firm Arup, which lost approximately $25 million after attackers used deepfake video technology to impersonate company executives, according to Reuters.
[LINK: Reuters – Arup deepfake fraud]
The attack began with a phishing email sent to an employee in Arup’s Hong Kong finance department requesting an urgent transfer. The employee initially suspected the request was fraudulent.
However, the attackers escalated the deception by inviting the employee to a video conference that appeared to include the company’s CFO and other executives. In reality, the meeting used AI-generated deepfake video and audio built from publicly available media.
Believing the executives were legitimate, the employee authorized the transfers.
Research from the University of Waterloo found that humans correctly identify sophisticated deepfake videos only about 24.5% of the time.
What this attack revealed
Synthetic media now allows attackers to impersonate trusted individuals in real-time communication channels.
Lesson for security teams
Require out-of-band verification and multi-person approval for large financial transactions.
5. The “Phishmas” AI Phishing Surge
While some attacks relied on targeted social engineering, 2025 also saw a dramatic surge in large-scale phishing campaigns driven by artificial intelligence.
Threat analysts recorded a 14-fold increase in AI-generated phishing messages during the December holiday season, according to research from Hoxhunt.
By the end of 2025, AI-generated messages accounted for more than half of reported phishing campaigns, with attackers using generative AI to produce highly convincing emails that mimicked legitimate corporate communications.
These messages removed many of the traditional warning signs associated with phishing, such as poor grammar or formatting errors.
What this attack revealed
AI is rapidly scaling the volume and realism of phishing campaigns.
Lesson for security teams
Traditional awareness training alone cannot stop modern phishing attacks. Technical safeguards must reduce reliance on human judgment.
What Security Teams Should Take Away from the Biggest Phishing Attacks of 2025
The phishing campaigns of 2025 demonstrate how rapidly social engineering is evolving. Attackers are no longer limited to deceptive emails. Instead, they combine multiple communication channels, impersonation tactics, and automation tools to manipulate trust and compromise identities.
Three patterns stand out.
Phishing is now omnichannel
Attackers increasingly combine email, phone calls, messaging platforms, and SaaS workflows within the same campaign.
Identity is the primary target
Modern phishing campaigns focus on stealing credentials, tokens, or permissions that allow attackers to operate as legitimate users.
Many phishing campaigns ultimately escalate into account takeover fraud, when attackers reuse harvested credentials to access legitimate accounts. Understanding how these attacks unfold is critical for preventing them.
Human trust remains the central attack surface
Many successful attacks occur because attackers convincingly impersonate trusted colleagues, vendors, or executives.
Phishing-related breaches are also becoming more expensive. The average cost of a data breach reached $4.88 million in 2025, according to IBM’s Cost of a Data Breach Report.
For security teams, defending against modern phishing requires stronger identity protection and improved visibility into authentication activity across systems.
Predict ATOs, Identify Lured Customers and Prevent Phishing Preemptively
Phishing campaigns rarely end with the initial lure. Once credentials or authorization tokens are harvested, attackers move quickly to exploit them for account takeover.
Memcyco shifts protection earlier in the attack timeline. The platform exposes when real users interact with impersonation infrastructure and correlates those signals with activity on the legitimate site, giving security teams real-time visibility into active phishing campaigns, targeted customers, and suspicious devices attempting to exploit stolen credentials.
This enables organizations to identify affected users, predict likely account takeover attempts, and disrupt phishing-driven attacks before they escalate into fraud or data breaches.
Discover Memcyco’s analyst-endorsed technology and why global enterprises choose Memcyco → Request a demo
FAQs
1. What is a modern phishing attack?
Modern phishing attacks are coordinated, multi-channel campaigns that combine email, voice calls, messaging, and SaaS workflows to manipulate users and compromise identity. Instead of relying on a single lure, attackers guide victims through interactions that ultimately lead to credential theft, token abuse, or unauthorized access.
2. How do phishing attacks bypass MFA?
Phishing attacks don’t always “break” MFA, they often work around it. Techniques like adversary-in-the-middle (AiTM) phishing, OAuth abuse, and social engineering allow attackers to capture session tokens, relay authentication in real time, or trick users and support teams into granting legitimate access.
3. Why are phishing attacks harder to detect today?
Modern phishing attacks blend into legitimate user behavior. When attackers use real credentials, authorized OAuth connections, or valid sessions, activity can appear normal during authentication. This creates a detection gap where malicious access is not flagged until later, if at all.
4. What is the link between phishing and account takeover (ATO)?
Phishing is one of the primary entry points for account takeover. Once attackers obtain credentials, tokens, or permissions, they can access real accounts as legitimate users. Many phishing campaigns are designed specifically to enable ATO, rather than just steal information.
5. What are the most common phishing channels today?
Phishing is no longer limited to email. Common channels now include voice phishing (vishing), SMS and messaging apps, SaaS and OAuth abuse, deepfake impersonation, and QR code phishing (quishing). Attackers often combine multiple channels within a single campaign.
6. How can organizations detect phishing before account takeover occurs?
Effective detection requires visibility before and during authentication, not just after login. Organizations need to identify users interacting with impersonation infrastructure, recognize suspicious device or session behavior, and correlate these signals with login activity to detect and stop attacks before account takeover happens.